If you have bought Bitcoin or any other cryptocurrency, one of the first decisions you face is where to keep it. That answer almost always comes down to one of two things: a hot wallet or a cold wallet. Most beginners end up with a hot wallet before they even think about it, because exchange accounts, browser extensions, and smartphone apps are all hot wallets by default.
This guide explains what a hot wallet is in crypto, how private keys work inside one, what the risks actually look like based on recent numbers, which wallets hold up best in practice, and how to use one without putting your funds at unnecessary risk.
What Is a Hot Wallet in Crypto?
A hot wallet is a software-based crypto wallet that stores your private and public keys on a device connected to the internet. It can take the form of a mobile app, a browser extension, a desktop program, or an account you hold on a crypto exchange. The defining feature is that the internet connection stays active, which makes sending and receiving funds fast and straightforward but also leaves those keys exposed to online threats around the clock.

The term “hot” refers to a live, active connection, the same logic behind calling a stove hot when it is running. A cold wallet, by contrast, stores keys on a device that stays offline and only connects briefly when you need to sign and send a transaction.
One point worth clearing up early: a crypto wallet does not store your coins. Your Bitcoin or Ethereum exists on the blockchain. What the wallet holds is the private key that proves you own those coins and gives you the ability to move them. If the private key is lost, the coins are gone. If someone else gets hold of it, they can drain the wallet from anywhere in the world within seconds.
How a Hot Wallet Works
Every crypto wallet, whether hot or cold, operates on a pair of cryptographic keys:
- Public key – works like a bank account number. You share it with anyone who needs to send you crypto. It generates your wallet address on the blockchain.
- Private key – works like a PIN or password. It signs transactions and proves ownership. It should never be shared with anyone under any circumstances.
When you set up a non-custodial hot wallet for the first time, it generates a seed phrase, usually 12 or 24 words in a specific order. That seed phrase encodes your private key. If your phone is lost or your computer is damaged, entering those words into a new installation of the wallet recovers full access to your funds. If someone else gets those words, they have the same access immediately, from any device, anywhere.
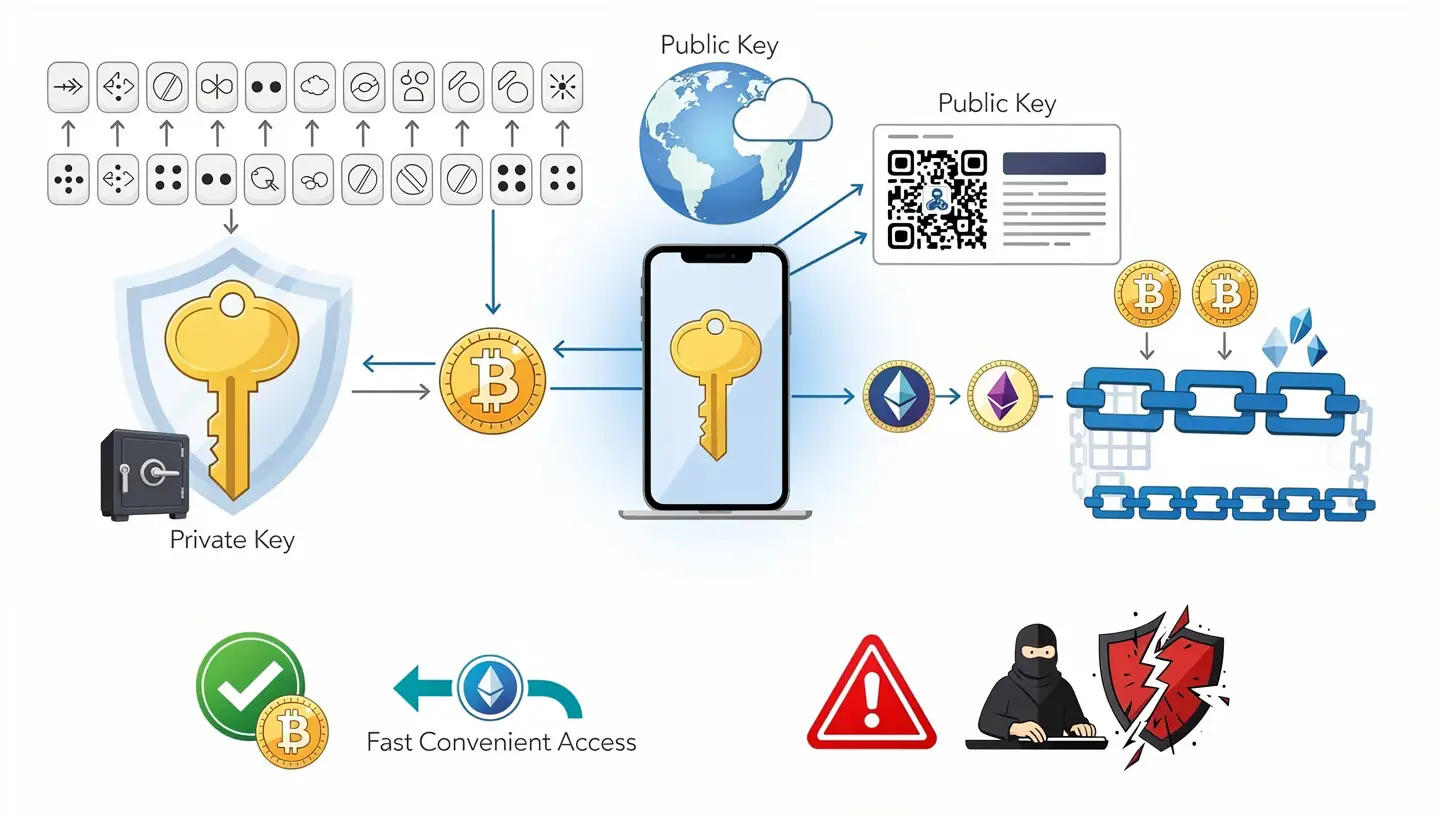
In a hot wallet, these keys are generated and stored on a device that is connected to the internet. That is the central trade-off: fast, convenient access in exchange for constant online exposure. To understand what that means for ownership and security, it helps to first understand what cryptocurrency actually is and how transactions on the blockchain confirm and record ownership.
Custodial vs Non-Custodial Hot Wallets
Not all hot wallets give you the same level of control. This is one of the most important distinctions in crypto and is often overlooked by new users.
A custodial hot wallet is one where a third party, usually a crypto exchange, holds your private keys on your behalf. You access your funds by logging in with a username and password. The exchange manages the keys and the infrastructure behind them. This is the arrangement on platforms like Coinbase, Binance, and Kraken when you use their built-in accounts. The advantage is simplicity. The risk is that you do not directly own your crypto in the same way. If the exchange is hacked, becomes insolvent, or freezes withdrawals, your funds are caught in the same situation. The phrase “not your keys, not your coins” exists because of exactly this arrangement.
A non-custodial hot wallet puts the private keys entirely under your control. The wallet software generates and stores them on your device. No company holds a copy. You are responsible for keeping the seed phrase safe. If you lose it and lose access to the device, the funds are gone permanently. The trade-off is that you have genuine ownership of your crypto, independent of any platform.
This distinction matters far more than which specific wallet app you pick. Understanding how crypto transactions actually work on the blockchain makes the difference between these two models easier to grasp in practice.
Types of Hot Wallets
Hot wallets come in four main forms. Each carries a different level of convenience and a different security profile.
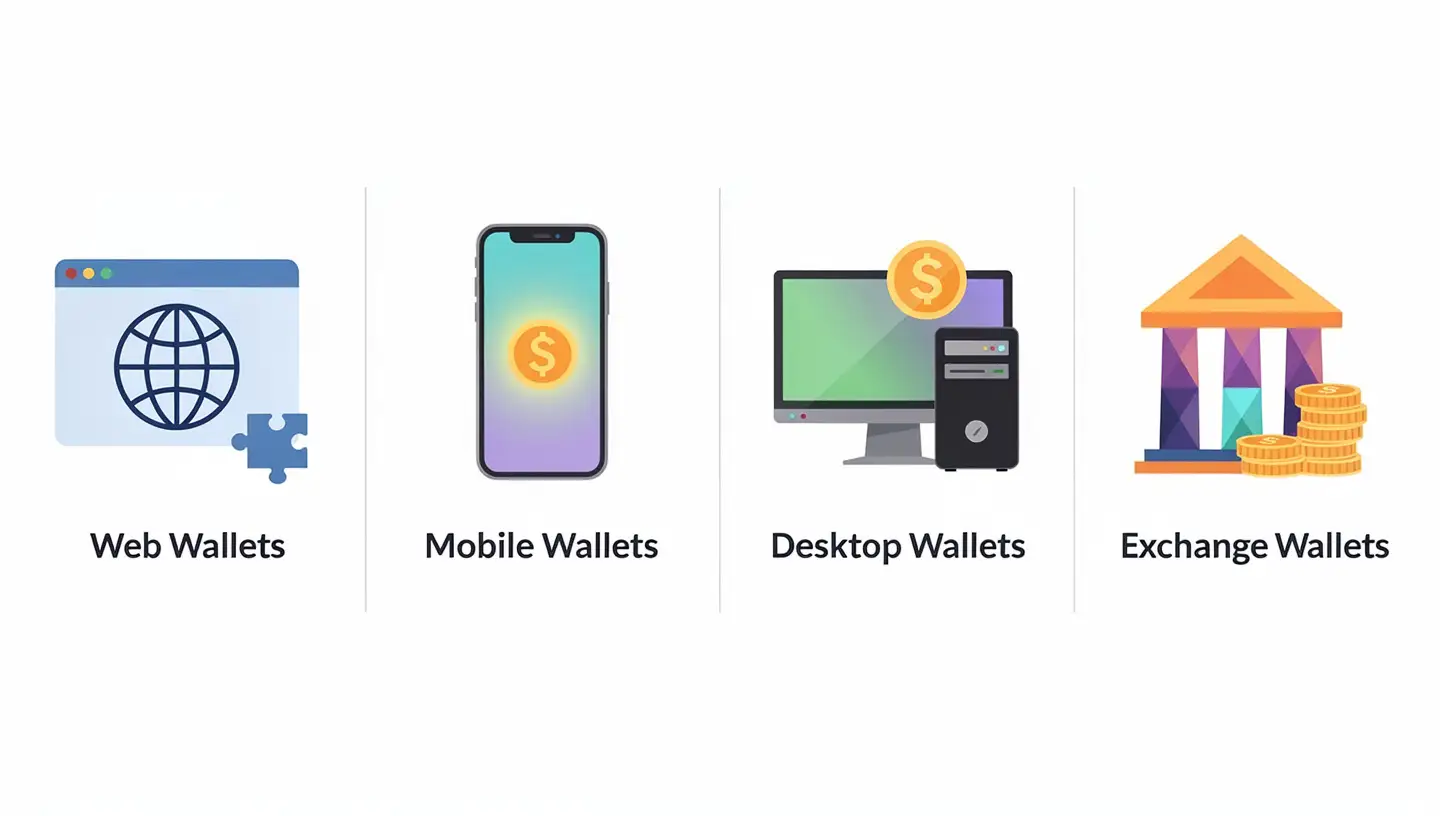
Web Wallets
Web wallets run inside a browser, either as an extension or through a website. MetaMask is the most widely used example. Browser extension wallets store your private key in the browser’s local data store and are non-custodial, meaning you hold the keys yourself. Cloud-based web wallets, such as an exchange login page, are custodial. The difference between those two has significant practical consequences if something goes wrong.
Mobile Wallets
Mobile wallets are apps installed on a smartphone. They store private keys directly on the device and are almost always non-custodial. Trust Wallet, Phantom, and Exodus mobile are common examples. They are the most popular choice for everyday use because they are portable, fast, and relatively simple to set up.
Desktop Wallets
Desktop wallets are programs that run on a laptop or PC and store keys on the hard drive. Exodus desktop and Atomic Wallet fall into this category. They are slightly more isolated than browser extensions because they do not operate inside another application, but any malware present on the same machine puts them at the same level of risk.
Exchange Wallets
Exchange wallets are accounts on trading platforms like Binance or Coinbase. These are custodial by definition. The exchange holds your private keys. You log in with credentials, not a seed phrase. They are the easiest entry point for someone new to crypto and practical for active trading, but they carry the highest counterparty risk of any wallet type. For a broader picture of how Bitcoin compares to other cryptocurrencies in terms of storage and ownership, the differences between wallet types become easier to put in context.
Hot Wallet vs Cold Wallet: Key Differences
The comparison between hot and cold wallets comes up in almost every conversation about crypto security. Here is how they stack up across the most relevant points:
| Feature | Hot Wallet | Cold Wallet |
|---|---|---|
| Internet connection | Always online | Offline by default |
| Private key storage | On internet-connected device | On offline hardware or paper |
| Security level | Moderate – exposed to online threats | High – isolated from online threats |
| Ease of use | High – fast transactions, always accessible | Lower – extra steps required to move funds |
| Cost | Usually free | $50 to $300 for a hardware device |
| Best suited for | Active trading, DeFi, smaller amounts | Long-term storage, large holdings |
| Recovery | Via seed phrase (non-custodial only) | Via seed phrase |
| Custodial option | Yes – exchange accounts | No – always self-custody |
It is also worth noting a third category that some institutions use: a warm wallet. Warm wallets keep private keys online and allow automated transaction creation, but require a human sign-off before a transaction is actually sent to the blockchain. This adds a security checkpoint without the full inconvenience of cold storage. Most individual users will not encounter warm wallets directly, but the concept explains why large exchanges and funds do not rely entirely on either hot or cold arrangements.
Most individual investors settle on a combination: a hot wallet for day-to-day activity, and a cold hardware wallet for assets they are not actively trading.
Hot Wallet Risks: What the Numbers Show
The convenience of a hot wallet has a measurable cost. In 2024, crypto hacks resulted in $2.2 billion in losses. Access control exploits, meaning stolen or misused private keys and seed phrases, accounted for roughly 78% of all crypto theft that year. Smart contract vulnerabilities, which dominated headlines in earlier years, fell to around 27% by comparison. Attackers have shifted their focus to private keys because that is where actual funds can be accessed and moved.
In the first half of 2025 alone, total losses from crypto services reached $1.93 billion. The February 2025 Bybit breach saw approximately $1.4 billion drained from multisig wallets, the largest single crypto theft ever recorded. Phemex lost around $85 million from hot wallets in January 2025 through what investigators described as a private key compromise. The Nobitex breach in June 2025 cost between $80 and $90 million from hot wallets, while cold wallets on the same platform were not affected.
These are exchange-level numbers, but individual users face the same attack methods on a smaller scale every day.
Phishing Attacks
Attackers build copies of wallet websites or apps and push traffic to them through ads, emails, and social posts. A user enters their seed phrase on what looks like the official site and the wallet is drained within minutes. In one 2022 case, a fake MetaMask site cost users more than $10 million in ETH. In 2024, a single phishing campaign targeting one crypto holder pulled $55 million in a single transaction.
Malware and Compromised Updates
Keyloggers, clipboard hijackers, and screen-capture tools can extract private keys or seed phrases from a device without any action from the wallet provider. In 2023, a malicious version of Atomic Wallet was distributed through a compromised update channel. When users installed it and entered their seed phrases, the malware transmitted those phrases to the attackers. Over $100 million was drained from roughly 4,100 addresses in that incident.
Exchange Failures and Custodial Risk
Custodial hot wallets carry a risk that has nothing to do with hacking: the platform itself can fail. If an exchange becomes insolvent, freezes withdrawals, or is taken offline, access to funds held there disappears with it. Users with non-custodial wallets are not affected by exchange failures because their keys live on their own devices.
Seed Phrase Exposure
Taking a photo of a seed phrase, storing it in cloud notes, or typing it into any website other than the official wallet recovery screen is one of the most common causes of individual fund loss. Once a seed phrase has existed on an internet-connected device or service, there is no way to confirm it has not been recorded or accessed.
Malicious Smart Contract Approvals
When connecting a hot wallet to a decentralized application, users are asked to approve token permissions. Approving unlimited spend from an unknown or malicious contract gives that contract the ability to drain a wallet without any further action from the user. This is one of the most common attack surfaces in DeFi and NFT platforms.
The rules of crypto ownership mean that a transaction confirmed on the blockchain cannot be reversed. There is no fraud department and no chargeback system. Once funds leave a wallet through a signed transaction, they are gone. Understanding why what BTC is and how Bitcoin ownership functions matters here puts that in concrete terms.
Best Hot Wallets in 2025 and 2026
The right hot wallet depends on which blockchain you use most, how often you trade, and how you weigh convenience against security controls. The five options below consistently rank highest across security architecture, active development, user adoption, and track record.
| Wallet | Best For | Chains Supported | Custodial | Cost |
|---|---|---|---|---|
| MetaMask | DeFi, Ethereum, Web3 | EVM + Solana + BTC | No | Free |
| Trust Wallet | Multi-chain, mobile users | 110+ blockchains | No | Free |
| Exodus | Beginners, desktop users | 50+ blockchains | No | Free |
| Phantom | Solana, NFTs | Solana, ETH, Polygon, Base | No | Free |
| Coinbase Wallet | Beginners, Coinbase users | EVM + BTC + SOL | No | Free |
MetaMask
MetaMask was launched in 2016 by ConsenSys and is used by around 30 million active users monthly as of mid-2025. It is available as a browser extension and a mobile app. Private keys are stored locally and encrypted on the user’s device and are never sent to external servers.
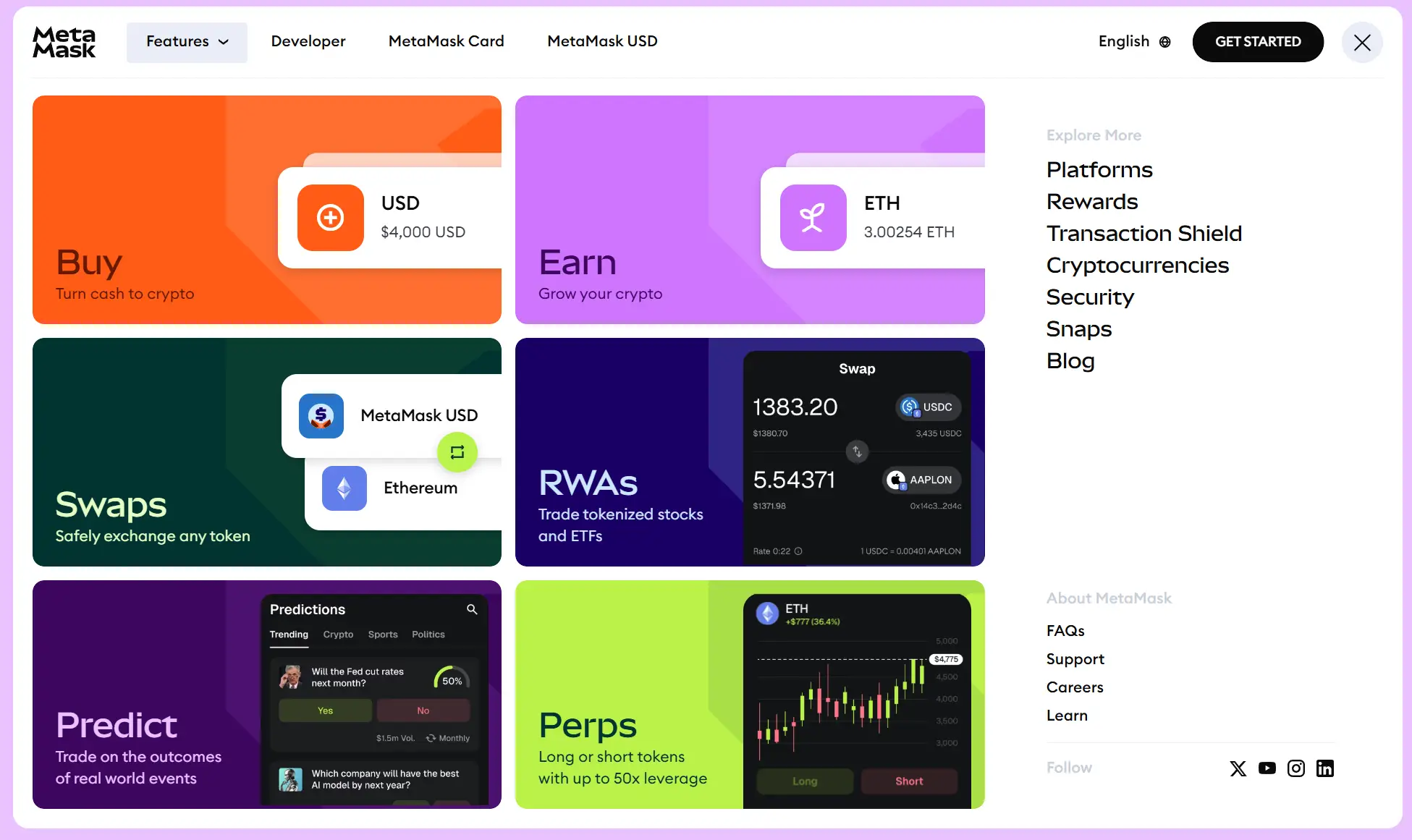
Its primary strength is tight integration with Ethereum and EVM-compatible chains, making it the default connection method for most DeFi platforms, NFT marketplaces, and Web3 applications. In 2025, MetaMask added native Bitcoin support and rolled out Multichain Accounts for managing assets across EVM chains, Solana, and Bitcoin from a single interface. It supports hardware wallet pairing with Ledger and Trezor, which adds a meaningful security layer for larger holdings.
Best for: DeFi users, Ethereum-heavy portfolios, advanced Web3 interaction.
Trust Wallet
Trust Wallet supports over 110 blockchains, the broadest coverage of any wallet on this list. It is non-custodial, stores keys on the device, and includes biometric locks alongside a real-time security scanner that blocked more than $162 million in potentially harmful transactions in 2025. The built-in dApp browser on mobile allows direct interaction with decentralized applications.
Staking for major assets is available directly inside the app. Trust Wallet had surpassed 220 million total downloads by the end of 2025. Desktop access is more limited than mobile, but mobile functionality is strong across the board.
Best for: Mobile users, multi-chain portfolios, straightforward everyday use.
Exodus
Exodus recorded a 92% approval rating among beginners in a 2025 user survey. It runs on desktop, mobile, and as a browser extension, supports over 260 assets, and includes built-in portfolio tracking.

In 2025, it introduced a Passkeys Wallet using biometric authentication as an alternative to a seed phrase, and XO Pay for buying crypto directly with a debit or credit card inside the app. It pairs with Trezor and Ledger for users who want cold storage alongside their software wallet. One gap worth noting: Exodus does not support traditional two-factor authentication.
Best for: Beginners and long-term holders who want a clean multi-asset experience on any platform.
Phantom
Phantom was built primarily for Solana and remains the strongest choice for anyone working in that network. It expanded in 2025 to support Ethereum, Polygon, Base, and Sui, and carries a 4.8 out of 5 rating on Google Play as of March 2026. NFT management is a standout feature, including a Burn NFT tool that removes unwanted tokens from a wallet.
Speed and simplicity within its supported networks are its main advantages over broader multi-chain options.
Best for: Solana users, NFT traders, anyone who wants a fast and focused mobile experience.
Coinbase Wallet
Coinbase Wallet is a separate product from the main Coinbase exchange app and is fully non-custodial. In 2025, it introduced passkey-based authentication through Face ID and Touch ID, allowing new users to set up without a traditional seed phrase. A smart wallet framework now supports creating up to 15 sub-wallets under a single recovery mechanism.
DApp activity grew 30% in the first half of 2025, and it connects directly to Coinbase’s exchange infrastructure for users moving between trading and self-custody.
Best for: Coinbase users moving to self-custody, beginners who want a familiar starting point with a recognised brand.
How to Use a Hot Wallet Safely
The risks tied to hot wallets are real, but most of them are avoidable with consistent habits. These are the practices that make the biggest practical difference:
- Write your seed phrase on paper and store it offline. Never photograph it. Never type it into any app, website, or message other than the official wallet during a recovery. This single habit prevents the majority of individual fund losses.
- Enable two-factor authentication (2FA). For custodial wallets and exchange accounts, 2FA stops most credential-based attacks. An authenticator app is more secure than SMS codes.
- Keep wallet software up to date. Software updates regularly patch security vulnerabilities. Running an outdated version of a wallet app is one of the more avoidable risks.
- Only download wallet apps from official sources. Go directly to the provider’s official website and follow their link to the app store. Fake wallet apps distributed through search ads are a common attack method.
- Only keep what you actively need in a hot wallet. Move larger amounts to a hardware wallet. The general guidance from security firms and exchanges alike: treat a hot wallet like cash in a pocket, not a savings account.
- Never share your private key or seed phrase with anyone. No legitimate wallet provider, exchange, or support team will ever ask for it.
- Review what you are signing before approving any transaction. Unlimited token spend approvals on unknown contracts are one of the most exploited attack surfaces in DeFi.
- Consider a multi-signature (multisig) setup for larger amounts. A multisig wallet requires more than one key to authorise a transaction, which limits the damage if a single key is compromised.
How to Choose the Right Hot Wallet
The best hot wallet for any individual depends on a few practical factors: which blockchains you use most, how often you transact, whether you prefer mobile or desktop access, and how comfortable you are managing your own private keys.
If you are primarily on Ethereum and use DeFi or NFT platforms regularly, MetaMask is the established standard. If you hold assets across many different chains and want everything in a single smartphone app, Trust Wallet covers the widest range with the least setup. For beginners who want a clean experience without technical complexity, Exodus or Coinbase Wallet are consistently rated highest for onboarding. For Solana-focused users, Phantom is purpose-built and well-regarded.
Before putting real money in any wallet, a few checks are worth making: confirm the team has a public track record, check whether the wallet has been independently audited, look at whether the code is open-source, and see how the provider has responded to past security incidents.
Many experienced users run two or three wallets at the same time: a hot wallet for active trading and DeFi, a hardware wallet for long-term storage, and sometimes an exchange account for buying and selling. That is how most people end up managing their crypto once they understand the trade-offs. To understand how Bitcoin fits into that picture as the most widely held digital asset, the fundamentals of what separates it from other coins is a useful place to start.
Frequently Asked Questions
What is a hot wallet in crypto?
A hot wallet is a software wallet that stores your crypto private keys on a device connected to the internet. It can be a mobile app, a browser extension, a desktop program, or a custodial account on a crypto exchange. Hot wallets make sending and receiving cryptocurrency fast and accessible, but the constant internet connection means the keys inside are exposed to online threats like phishing attacks and malware.
Is a hot wallet safe to use?
Hot wallets carry more risk than cold wallets because the private keys are stored on internet-connected devices. That does not make them inherently unsafe, but it does mean the margin for error is smaller. Keeping only what you actively need in a hot wallet, storing your seed phrase offline, keeping software updated, and enabling two-factor authentication where available reduces the risk considerably. For large holdings or long-term storage, a cold wallet is the safer option.
What is the difference between a hot wallet and a cold wallet?
The core difference is internet connectivity. A hot wallet stores private keys on a device that is always online, making transactions fast and accessible but leaving keys exposed to potential attacks. A cold wallet stores keys on a device that stays offline, protecting them from online threats but requiring extra steps to move funds. Hot wallets are almost always free. Cold hardware wallets typically cost between $50 and $300.
What is the difference between a custodial and non-custodial hot wallet?
A custodial hot wallet is one where a third party, usually a crypto exchange, holds your private keys on your behalf. You access funds through login credentials. A non-custodial hot wallet stores your private keys on your own device, giving you direct control. Non-custodial wallets require you to manage your seed phrase securely, but your funds are not affected if the platform goes down or is hacked.
What happens if I lose access to my hot wallet?
If you lose the device your non-custodial hot wallet is installed on, you recover access using your seed phrase. Entering those 12 or 24 words into any compatible wallet app restores full access to your funds. If you lose both the device and the seed phrase, the funds are permanently inaccessible. There is no recovery service that can retrieve them. For custodial wallets on exchanges, account recovery options like password reset may be available.
Can a hot wallet be hacked?
Yes. Hot wallets can be compromised through phishing attacks, malware on the device, fake wallet apps, or in the case of exchange wallets, through a breach of the exchange’s own infrastructure. In 2024, compromised private keys accounted for roughly 78% of all stolen crypto. Using a non-custodial wallet, keeping your seed phrase offline, and being careful about what transactions you approve reduces this risk considerably.
What is the best hot wallet for beginners?
Exodus and Coinbase Wallet are consistently rated highest for beginners based on their interfaces and onboarding experience. Trust Wallet is also beginner-friendly with broad multi-chain support. For anyone focused on Ethereum and DeFi, MetaMask is the standard starting point. The best choice depends on which assets you hold and how you plan to use them.
Should I keep my crypto on an exchange or in a hot wallet?
Keeping crypto on an exchange means the exchange controls your private keys. If the exchange is hacked, becomes insolvent, or freezes withdrawals, your funds are affected. A non-custodial hot wallet keeps the keys on your device, giving you direct ownership. For anything beyond short-term trading, moving funds to a wallet where you hold the keys directly is the more secure approach. The phrase used across the industry sums it up: “not your keys, not your coins.”